WinjaCTF at c0c0n [2021]: I developed an easy challenge - called “Anonymous” - the challenge was based upon browser forensics.
TL;DR
Intended Way - Download the zip > Extract it > Navigate the Linux directory structure > To find a directory called .config > google-chrome > Default > Open the History File in SQL Browser > Search for URLs and upon up the URL to get a file with the name - formatted like flag.
Un-Intended Ways - Too Many 😂
Detailed WriteUp
Download the ZIP and from the description it is obvious that it’s a forensics challenge.
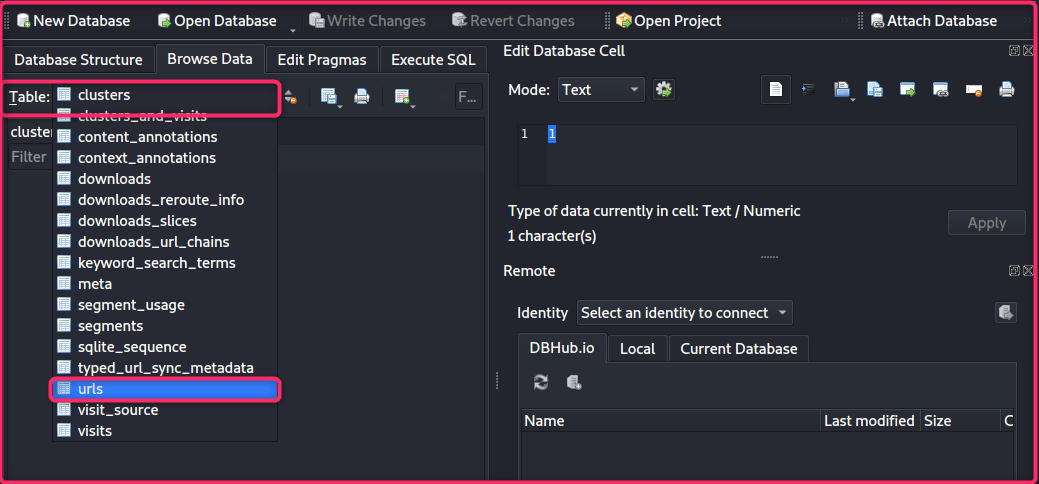
Navigate to /home/crazy_crocodile/.config/google-chrome/Default/ and Open the “History” file in SQLite Browser.
Note:
.config/google-chrome/Default/contains all the chrome relatead artifacts
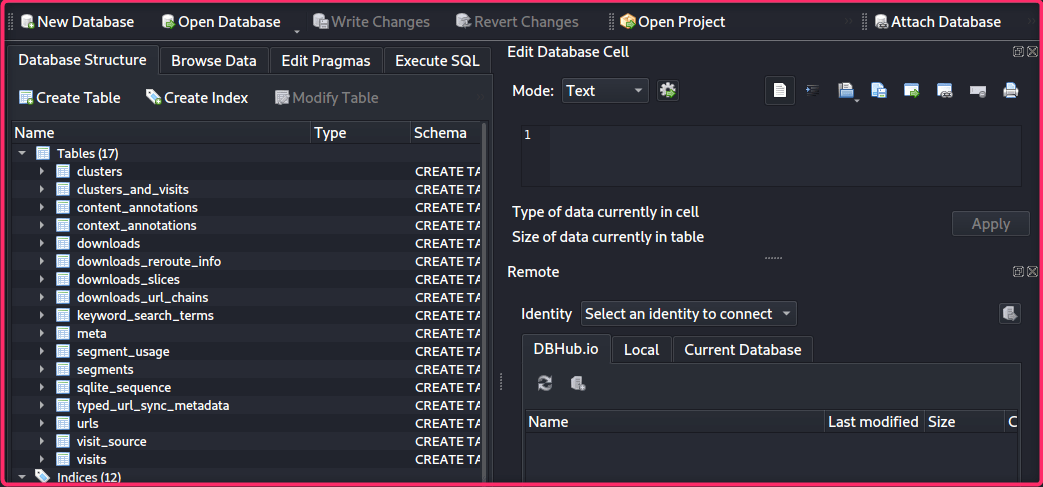
Click on the Browse Data Tab > Change the Table Dropdown to urls
Get the Drive URL or See the Filter tab to get the file name.
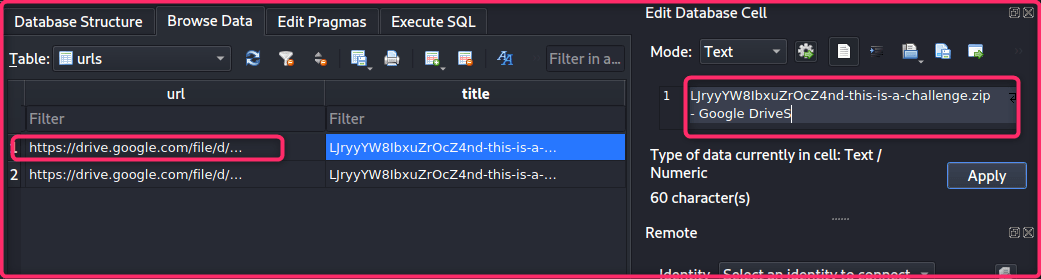
Final Flag:
flag{LJryyYW8IbxuZrOcZ4nd-this-is-a-challenge}
Thanks for playing Winja CTF 2020!